You must follow these steps completely and in the order shown. Failure to do so increases the risk of node failure.
In this section....
For details on troubleshooting, see Troubleshooting Cloud Connector 6.1.2.
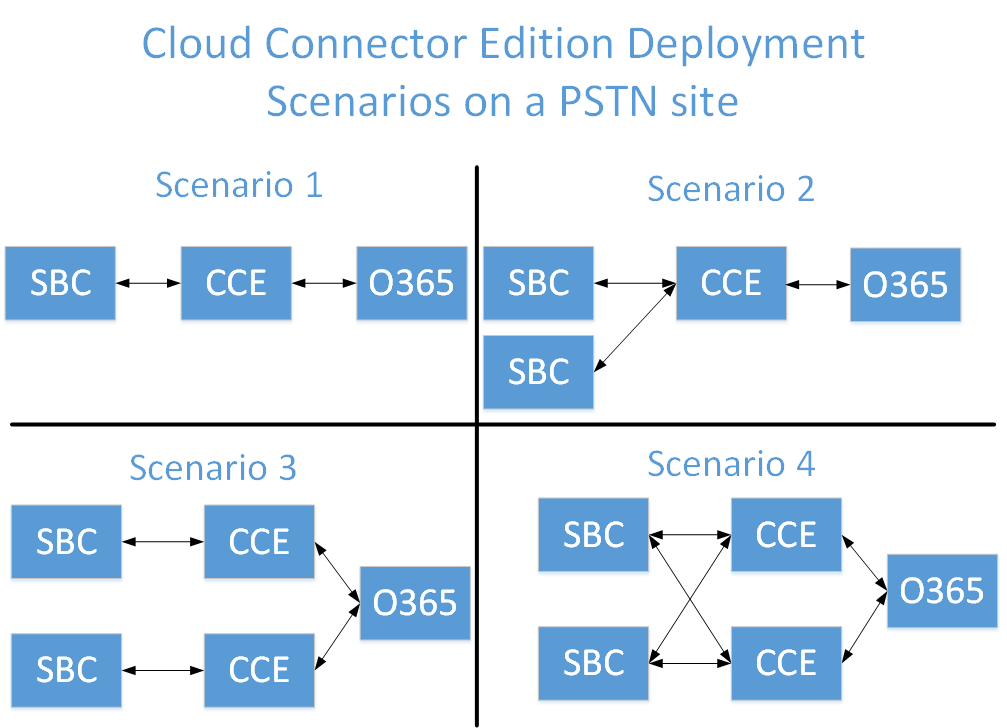
This page provides a step-by-step procedure for Non High Availability Deployment on SBC Edge CCE. The following diagram shows typical CCE deployment scenarios on a PSTN site. The PSTN site is a combination of Cloud Connector instances, deployed at the same location, and with common PSTN gateways pool connected to them. PSTN sites allow you to: Provide connectivity to gateways that are closest to your users. Allow for scalability by deploying multiple Cloud Connector instances within one or more PSTN sites. Allow for high availability by deploying multiple instances of Cloud Connector within a single PSTN site. CCE Deployment Scenarios
Before You Start
CCE Deployment Scenarios
Scenario 3 and Scenario 4 are covered in Configuring the SBC Edge for Two CCEs. This document contains steps for Scenario 1 and Scenario 2 deployments. Prerequisites An Office 365 tenant with an E5 license or E3 + Cloud PBX. You must have the Global Administrator role for your O365 tenant account. A public certificate authority ready to sign a certificate for the SBC Edge. Important! Read the steps outlined in Certificate Requirements at Microsoft Technet. A properly configured firewall. See Ports and Protocols at Microsoft Technet. Latest System Release SBC Firmware. Important! Latest System Release SbcComms Firmware. Important!Prerequisites
A public domain name prepared and mapped with your Office 365 tenant (for example, "mydomain.com"). See Create an Office 365 Tenant. An entry on your public domain name that points to the fixed IP address of your SBC Edge (for example, myccesite1.mydomain.com" with an IP address of "66.67.68.69"). Microsoft Cloud Connector Edition image on ASM recovery partition.
Network Settings
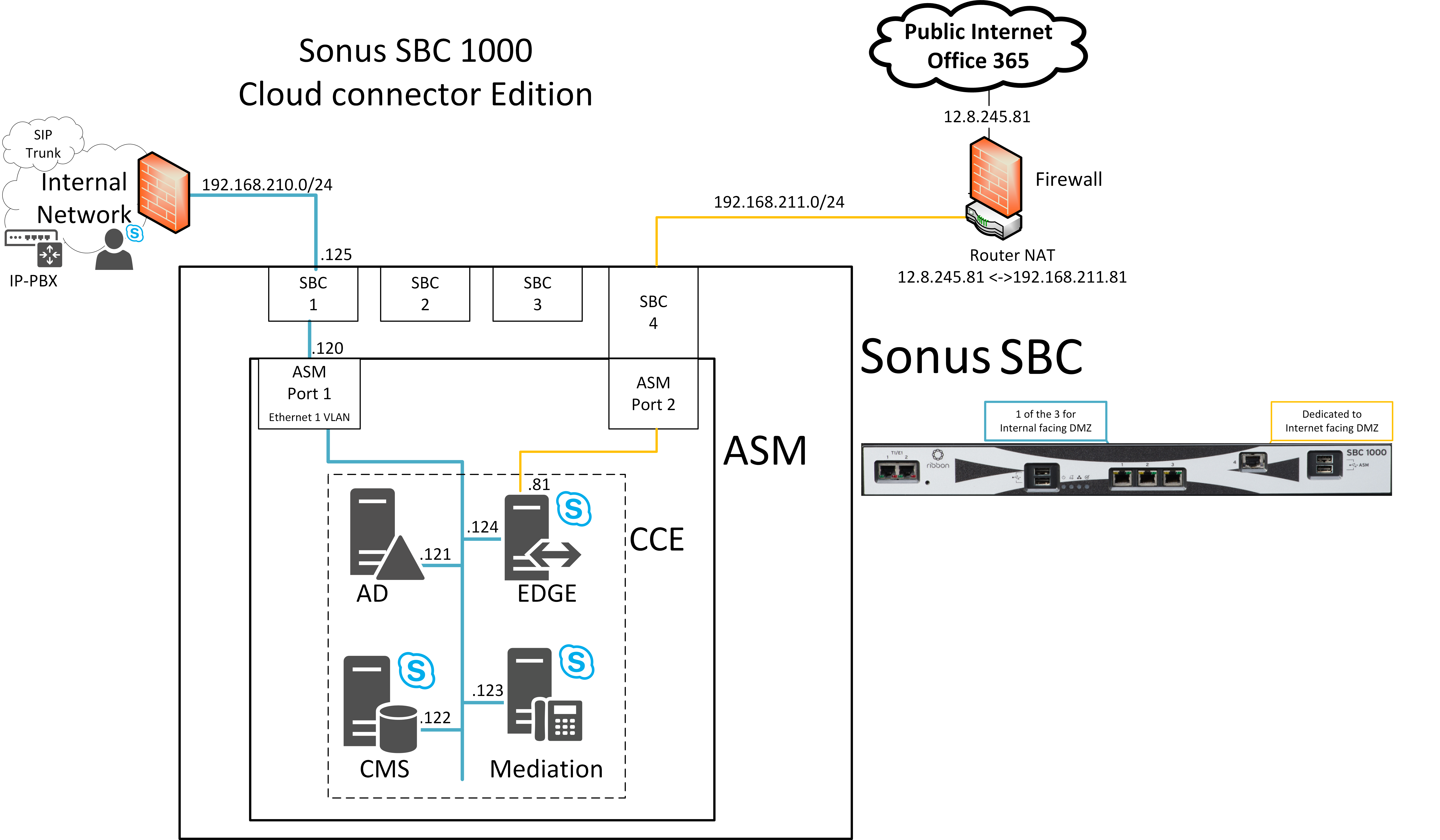
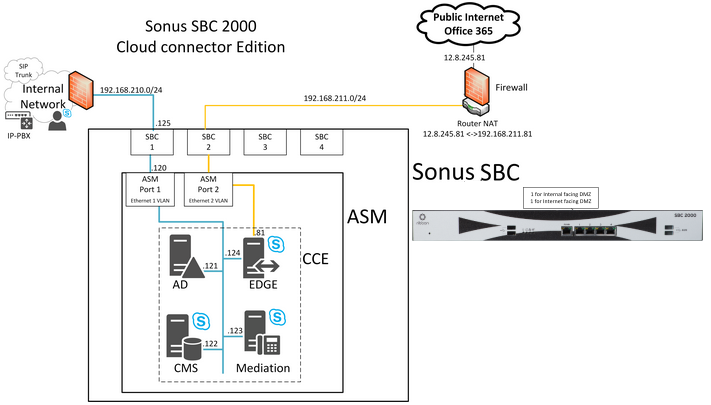
For this best practice, Cloud Connector Edition deployment follows the cabling shown below:
Typical Deployments
Firewall Settings
For this best practice, the Router/Firewall is configured using the following rules:
Internal Firewall Rules
| Source IP | Destination IP | Source Port | Destination Port |
|---|---|---|---|
Cloud Connector Mediation component | Internal clients | TCP 49 152 – 57 500* | TCP 50,000-50,019 (Optional) |
Cloud Connector Mediation component | Internal clients | UDP 49 152 – 57 500* | UDP 50,000-50,019 |
Internal clients | Cloud Connector Mediation component | TCP 50,000-50,019 | TCP 49 152 – 57 500* |
Internal clients | Cloud Connector Mediation component | UDP 50,000-50,019 | UDP 49 152 -57 500* |
External Firewall Rules
Source IP | Destination IP | Source Port | Destination Port |
|---|---|---|---|
Any | Cloud Connector Edge External Interface | Any | TCP 5061 |
Cloud Connector Edge External Interface | Any | Any | TCP 5061 |
Cloud Connector Edge External Interface | Any | Any | TCP 80 |
Cloud Connector Edge External Interface | Any | Any | UDP 53 |
Cloud Connector Edge External Interface | Any | Any | TCP 53 |
Cloud Connector Edge External Interface | Any | TCP 50,000-59,999 | Any |
Cloud Connector Edge External Interface | Any | UDP 3478 | Any |
Cloud Connector Edge External Interface | Any | UDP 50,000-59,999 | Any |
Any | Cloud Connector Edge External Interface | Any | TCP 443 |
Any | Cloud Connector Edge External Interface | Any | TCP 50,000-59,999 |
Any | Cloud Connector Edge External Interface | Any | UDP 3478 |
Any | Cloud Connector Edge External Interface | Any | UDP 50,000 - 59,999 |
DNS Settings
Make sure that CCE FQDN is resolving to the
Preparing Your Node
Preparing the Unable to show "metadata-from": No such page "_space_variables" for Initial Setup
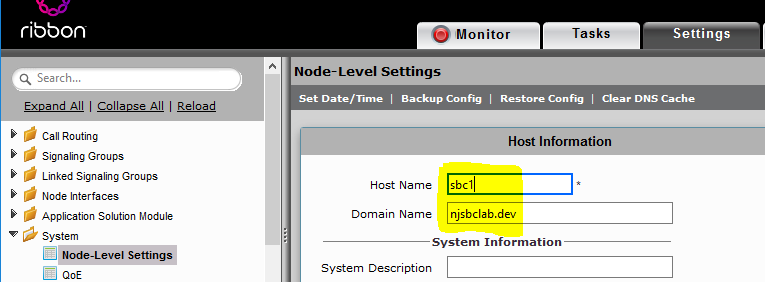
Update the
Ensure the Node FQDN is definitive. Changing this information requires the CCE to be redeployed.
Sonus recommends starting with a clean and empty configuration.
Ensure That the Node FQDN is Correct
Optionally, if you want to configure a secondary
Preparing the ASM
If your ASM have been used before, you should re-Initialize it now. Refer to Re-Initializing the ASM for details.
Confirm that the ASM is ready to deploy the Cloud Connector Edition. To do so:
| Step | Action |
|---|---|
| 1 | Login to the WebUI of the SBC Edge. |
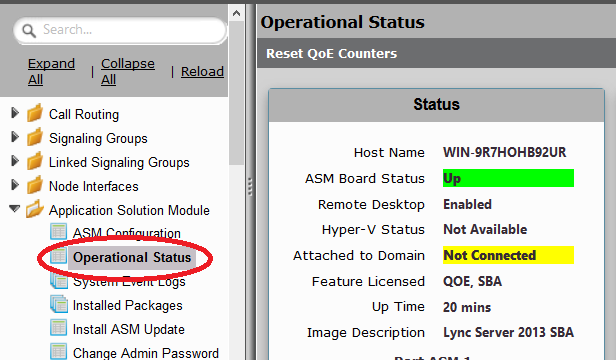
| 2 | Click the Task tab and then select Operational Status. |
| 3 | Verify the following:
|
Operational Status
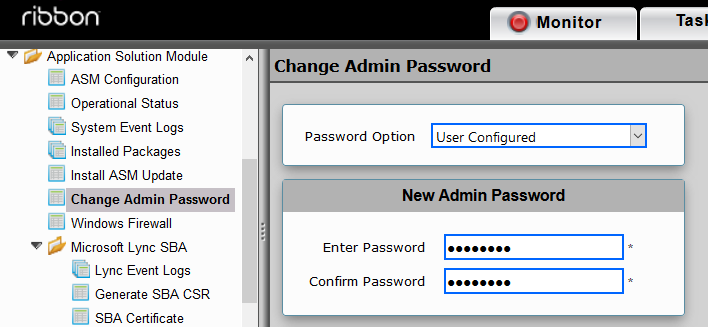
After you update the ASM, change its Admin Password.
| Step | Action |
|---|---|
| 1 | Login to the WebUI of the SBC Edge. |
| 2 | Click the Settings tab and then click Change Admin Password. |
| 3 | Enter and confirm your new password and then click OK. |
New Admin Password
Deploying the CCE
Deploying the CCE on the
- Setup CCE using the Unable to show "metadata-from": No such page "_space_variables"WebUI.
- Prepare the CCE deployment on the Unable to show "metadata-from": No such page "_space_variables"WebUI using the Sonus Cloud Link Deployer.
Configuring the CCE using the SBC Edge WebUI
- If this is a new CCE Deployment, proceed with Configuring the CCE Through the WebUI
- If this is a re-deployment of a CCE deployment, complete the steps in Redeploying the CCE to clean up previously entered data in O365 before proceeding with the following section.
Configuring the CCE Through the WebUI
ASM Config
| Step | Action |
|---|---|
| 1 | Login to the WebUI of the SBC Edge. |
| 2 | Navigate to Tasks > Setup Cloud Connector Edition. |
| 3 | Click the ASM Config tab and configure/verify the Network and IP settings of your ASM. |
| 4 | Click Apply. After receiving the activity status as successfully completed, click the Generate CSR tab. |
ASM Config
Generating the CSR
This process is required only if you don't have a public certificate for your deployment. If you already have a certificate, proceed to Import Certificate.
| Step | Action |
|---|---|
| 1 | Login to the WebUI of the SBC Edge. |
| 2 | Navigate to Tasks > Setup Cloud Connector Edition > Generate CSR. |
| 3 | Generate the CSR as shown below with following information. To ensure creating a valid CSR for Cloud Connector Edition usage, please see the section "Certificate requirements" on https://technet.microsoft.com/en-us/library/mt605227.aspx . |
| 4 | Copy the CSR from the lower pane of the Generate CSR page and save it as a .txt file. |
| 5 | After the CSR is signed by the Certificate Authority and you receive the PKCS7 Certificate file, continue the wizard by clicking on Import Certificate tab. |
Importing Certificate/Keys
| Step | Action |
|---|---|
| 1 | Login to the WebUI of the SBC Edge. |
| 2 | Navigate to Tasks > Setup Cloud Connector Edition and then click the Import Certificate/Keys tab. |
| 3 | Click the Action drop-down list and select the appropriate option:
|
| 4 | Select the relevant certificate file using the Choose File button and then click OK. |
| 5 | Select the file by browsing to it using Select File. |
| 6 | Click OK. |
| 7 | After receiving the activity status as successfully completed, click on Configure CCE tab. |
Configuring the CCE
| Step | Action |
|---|---|
| 1 | Login to the WebUI of the SBC Edge. |
| 2 | Open the Tasks tab and click Setup Cloud Connector Edition in the navigation pane. |
| 3 | Click the Configure CCE tab. |
| 4 | Configure all necessary information and then click OK. All the pre-configured fields are valid as is, and recommended by Sonus. These fields may be edited, but all entries must meet Microsoft requirements. If the deployment environment consists of multiple-site with a single certificate or a wild card certificate, ensure the CCE Site Name and the Edge Server Public Hostname are correct before proceeding. |
| 5 | After receiving the activity status as successfully completed, click the Prepare CCE tab to continue. |
Configure CCE
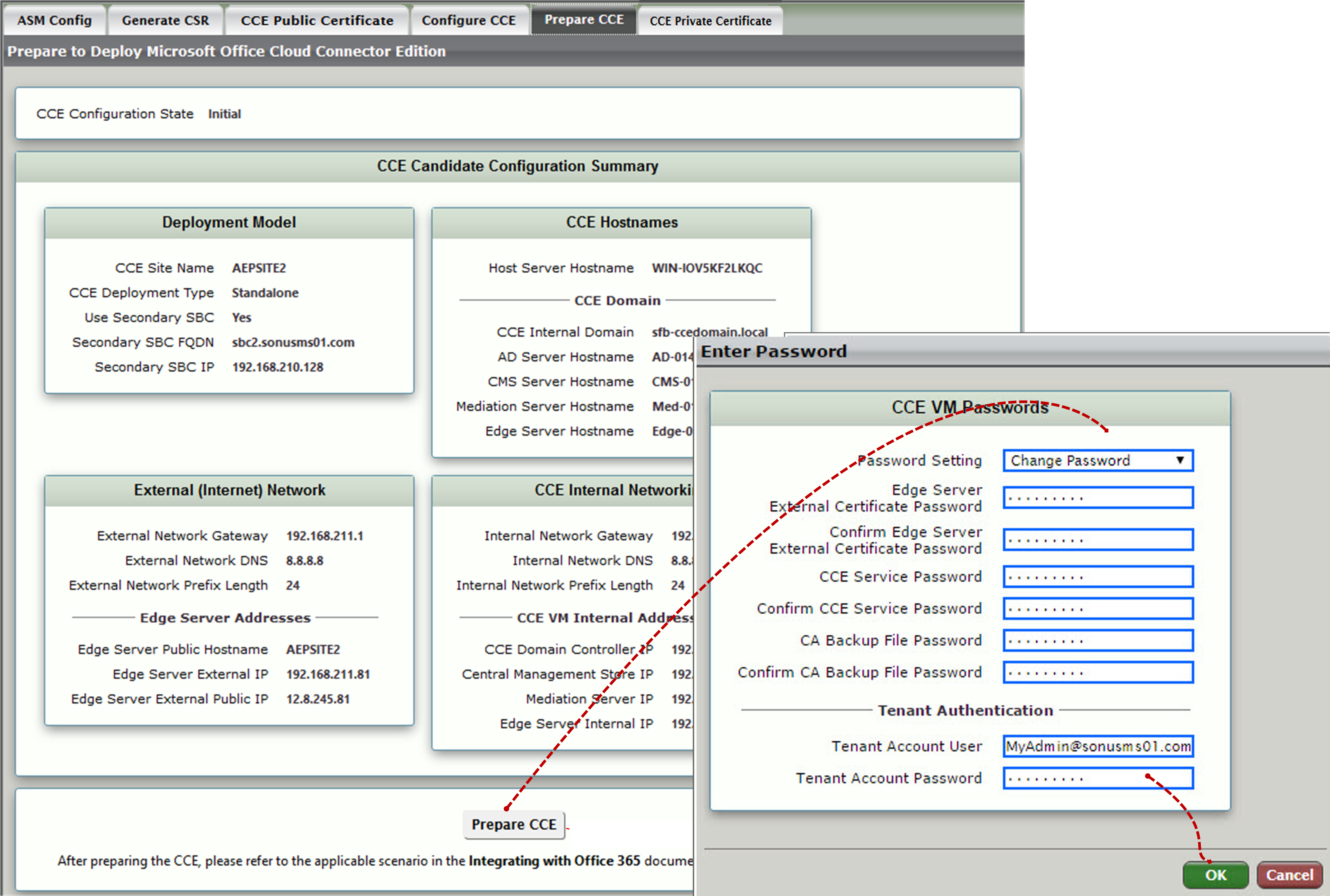
Preparing the CCE
| Step | Action |
|---|---|
| 1 | Login to the WebUI of the SBC Edge. |
| 2 | Open the Tasks tab and click Setup Cloud Connector Edition in the navigation pane. |
| 3 | Click the Prepare CCE tab. |
| 4 | Click the Prepare CCE button. Enter the requested password. A confirmation will request you to enter the password again. Click OK as shown below. |
| 5 | To complete the deployment, continue with installing the CCE Appliance using the Sonus Cloud Link Deployer. |
Prepare the CCE
Installing the CCE Appliance using Sonus Cloud Link Deployer
If you plan to use a proxy on the ASM Host to reach Office 365, you must add the Management network (192.168.213.0) into the exclusion list and specify proxy settings per machine rather than per user.
- The CCE deployment may exceed two hours.
- The CCE deployment status is visible only on the Remote Desktop to the ASM. The WebUI indicates that the CCE is running while the deployment process is in progress.
- While the CCE deployment is running, you should not perform any actions on the ASM via the WebUI (i.e., Shut Down/Reset/Reboot/Reinitialize/Install etc.).
| Step | Action |
|---|---|
| 1 | Remote desktop to the ASM system. |
| 2 | Launch the Sonus Cloud Link Deployer from icon on the desktop. |
| 3 | Check the first three actions:
Select Apply. |
Sonus Cloud Link Deployer
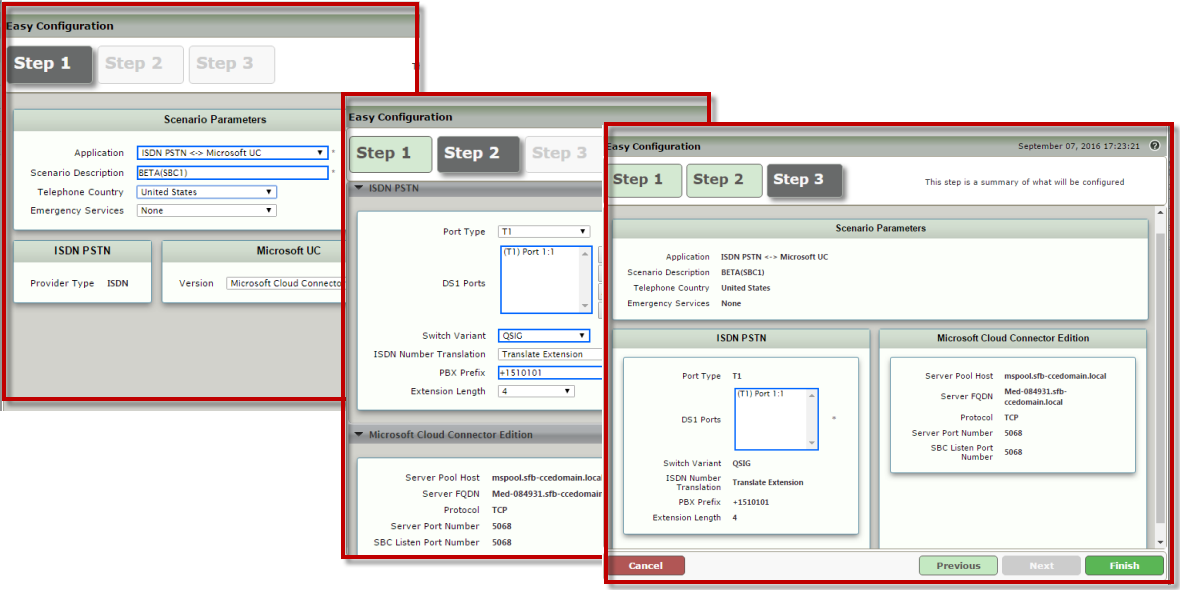
Integrating the SBC Edge With Cloud Connector Edition
After the CCE is deployed, integrate the Sonus SBC Edge and allow calls from/to O365 clients. In this example, the following steps will set up the Sonus SBC Edge for:
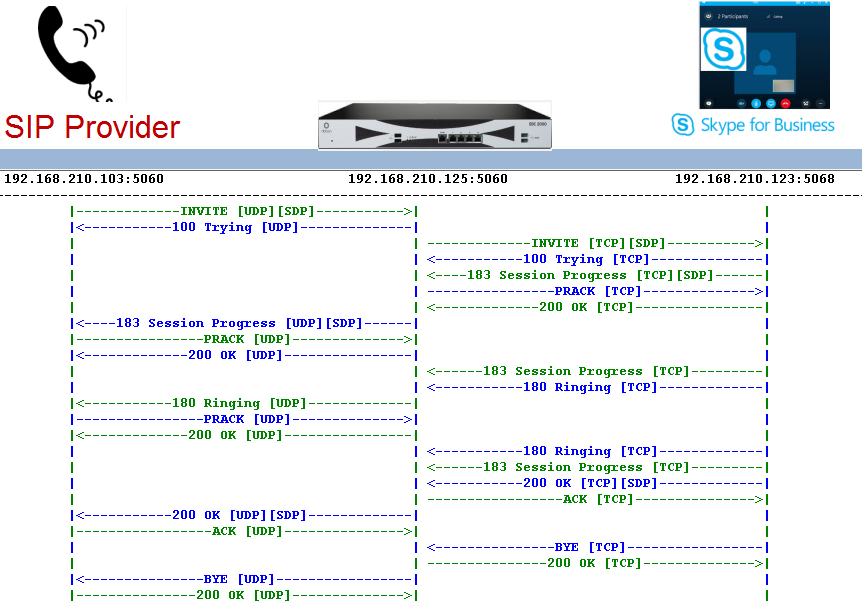
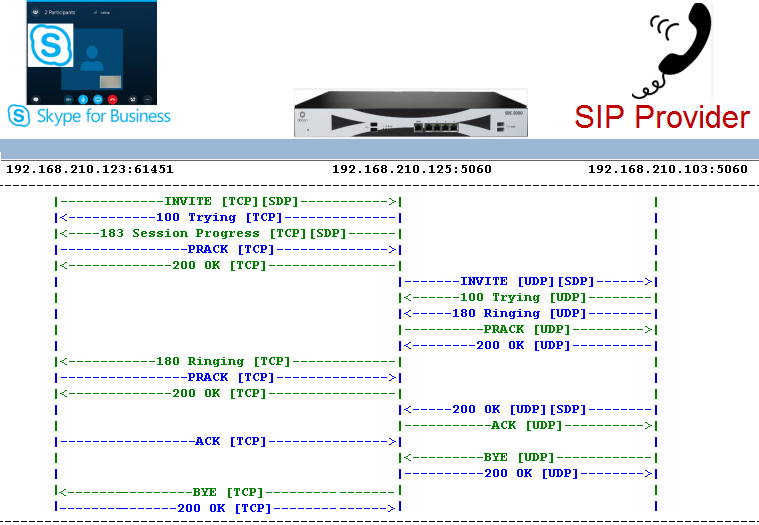
SIP Provider (193.168.210.103) – SBC Edge (193.168.210.125) – CCE (mediation Server: 193.168.210.123) – O365 Cloud |
Build your SBC configuration
| Step | Action |
|---|---|
| 1 | Login to the WebUI of the SBC Edge. |
| 2 | Click the Tasks tab, and then click SBC Easy Setup > Easy Config Wizard in the navigation pane. |
| 3 | Follow steps 1, 2, and 3 as shown below and then click Finish.
|
| 4 | Click OK on the next two popups to complete the setup. |
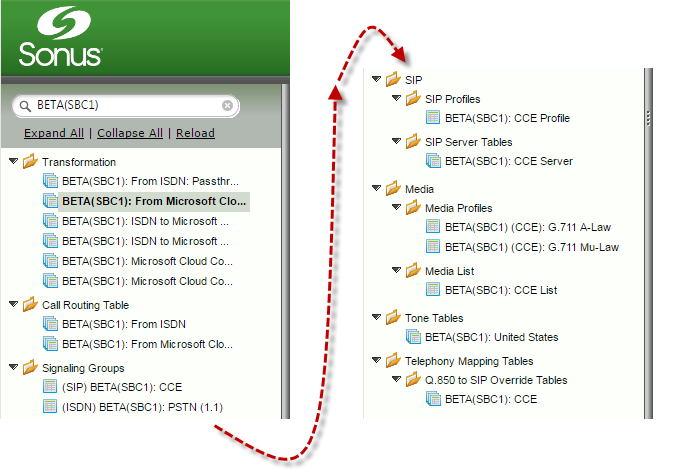
| 5 | The wizard configures the necessary settings for the single SBC Edge and CCE integration. Relevant configuration items are shown in the Settings tab below:
|
Build your Second SBC Configuration (Optional)
| Step | Action |
|---|---|
| 1 | Login to the WebUI of the Secondary SBC Edge. |
| 2 | Click the Tasks tab and then run the Easy Config. |
| 3 | The preceding step will configure the Secondary SBC Edge with the appropriate configuration items. |
With the preceding settings, an endpoint from the SIP provider side can dial the number of a Skype For Business (O365) client and reach out to it over Call Flow Similarly, a Skype For Business (O365) client can dial the number of an endpoint off of ITSP and reach out to it over Call Flow Configuration changes to the CCE in the WebUI per Tasks > Setup Cloud Connector Edition> Configure CCE requires the CCE to be re-deployed. Backup the Public Certificate per Tasks > Setup Cloud Connector Edition> Import Certificate. The ASM must be re-initialized with the image that contains the latest CCE software . To do so: Step Select the appropriate image from the drop-down list and then click Apply. If the CCE was previously deployed, previously installed information must be cleared in O365. To do so, follow the steps below: Connect the Office365 Tenant through a series of commands as follows: a. Execute the following command: Execute the following command to remove the appliance: Execute the following command to verify that the appliance has been removed: This completes the cleanup. Basic Call Verification after CCE Deployment and
O365 Known Issue and Workarounds for CCE
Redeploying the CCE
Re-Initializing of the ASM
Step Action 1 Login to the WebUI of the SBC Edge. 2 Click the Task tab, and then click Reinitialize in the navigation pane. 3 Clean Office 365 tenant
Step Action 1 Remote Desktop to the ASM system 2 Import-Module skypeonlineconnector$cred = Get-Credential$Session = New-CsOnlineSession -Credential $cred -VerboseImport-PSSession $session3 Display all the Appliances assigned to your tenant, identify the Appliance you just re-initialized, and copy the identity into your clipboard. Get-CsHybridPSTNAppliance4 Unregister-CsHybridPSTNAppliance -Identity <paste the identity here> -Force5 Get-CsHybridPSTNAppliance6
Manually Managing the CCE Configuration File
The “.ini” file is the configuration of the Microsoft CCE (Cloud Connector Edition) running on the ASM. The contents of the ".ini" file must be as defined by Microsoft. From the Configure CCE panel, the Raw INI Config drop-down list enables you to edit, export, or import the ".ini" file.
Working with the ".ini" file allows you to provision multiple CCEs in a similar manner. Once you configure a CCE, you can export the ".ini" file, modify it for the second system, and then import the CCE. This procedure can then be repeated for the third system, etc. Also, backing up the SBC configuration and CCE configuration helps recover faster in the case of lost data.
| Step | Action |
|---|---|
| 1 | After receiving the activity status completion message, click the Click to re-configure CCE application button. |
| 2 | Click OK on the popup. |
| 4 | Click the Raw (INI) Config drop-down list, select Edit. Configurable fields are displayed for editing. Modifications to the CCE configuration requires redeployment of the CCE VM, and this action takes approximately two hours. Note: The example uses AEPSITE2 for the these attributes. |
| 5 | After verifying the information click OK. |
Importing and Exporting the CCE Configuration File
Step | Action |
|---|---|
| 1. | After receiving the activity status completion message, click the Click to re-configure CCE application button. |
| 2. | Click OK on the popup. |
| 3. | From the Raw (INI) Config drop down list, select Import or Export.
|
Updating the CCE Password
Follow these steps if you need to update the O365 tenant admin password or account.
| Step | Action |
|---|---|
| 1 | On the WebUI, run Preparing the CCE to specify a new Password. Select the existing password and enter the new password. Only the O365 should be modified for a running instance of CCE. |
| 2 | On Remote desktop, start the Sonus Cloud Link Deployer, and check Transfer Password from SBC to reset the credentials. |