This document details a complete implementation of the SBC's RBA Feature
Prerequisites
Assumes the user is familiar with navigating the SBCx000's WebUI
The RBA feature requires the latest ASM image. Be sure that the HQ ASM is upgraded to the latest image version.
Install the Lync Server Resource Kit on the Lync Server. You will want the Bandwidth Policy Server Monitor Application to verify the dynamic CAC Profile changes. See the Microsoft Lync Server site to obtain the Resource Kit and installation instructions.
The RBA Feature is only supported between two Sonus SBC nodes
The RBA Feature requires an ASM installed on the HQ SBC
The RBA Feature is included only in SBC version 3.0 or newer.
SBC Configuration
This quick start document shows the steps and interlational parameters required to configure a UX to successfully route calls. The configuration process of a UX should always begin with running a wizard; however, the wizard only needs to be run for the very first configuration.
There are many different architectures which might be used for connecting remote sites to a main site. The manual pages for this 3G4G feature specify a VLAN switch with the 3G4G and WAN networks sharing a single port of the UX.
The implementation below uses a 3G4G router connected to the remote LAN segment, thus dedicating the WAN connection to a SBC port. This configuration elminates then need for a VLAN-capable switch.
Network Diagram
Network Diagram
Before Beginning
As a prerequisite to installing the RBA feature, check the following items:
- STUN Setting on the SBC
- Installed ASM Image
- RBA License
- DNS Configuration
STUN Setting
Configure Send STUN Packets to Enabled in the Media | Media System Configuration.
STUN Setting
RBA Image
If your HQ-side SBC was running version 2.2, you will need upgrade both the ASM image as well as the SBC firmware. The latest ASM image is available at support.net.com.
These instructions detail the use of an SBA image rather than the RBA image. Both images perform equivalent functions for the RBA implementations. In fact, a future SBC version will use a single image for both SBA and RBA. For now, you may use either the RBA or SBA image when installing the 3G4G Backnet feature.
Is your ASM running an SBA image compatible with your Lync Server? If you're running Lync 2013, be sure your ASM image is the Lync 2013 SBA image. The Lync 2013 SBA image is available from downloads.net.com.
Under the Tasks Tab | Application Solution Module | Reinitialize the pull-down selection will supply the possible images currently available on your ASM. Update your ASM images if you are implementing Lync Server 2013 and there is no Lync 2013 image available on your ASM.
Reinitialization
Check the RBA License
Verify that your SBC is licensed for the RBA feature.
Check RBA License
DNS Configuration
Add both SBCs to the DNS server. In the example, SBC2000 is the HQ SBC and SBC1000 is the remote network SBC. The DNS server is configured only with the LAN-side IP addresses of these nodes, 10.1.1.74 and 10.1.2.71, respectively.
Add the FQDNs and IP addresses for nodes that are part of the RBA feature:
- Remote-network SBC
- HQ SBC
- HQ ASM
- Lync Server
DNS Configuration
Lync Server Topology Configuration
The remote-network SBC must be added to the Lync Topology. Follow these steps:
- Open the Topology Builder
- Add a new Branch Site
- Add the SBC as a PSTN Gateway
Open the Lync Topology Builder
Start the Topo Builder
Start Topology Builder
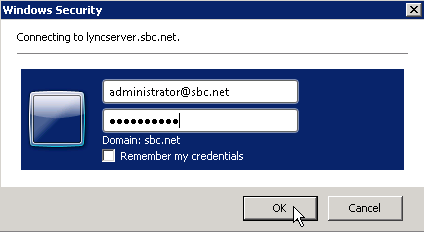
Enter Login Credentials
Login Credentials
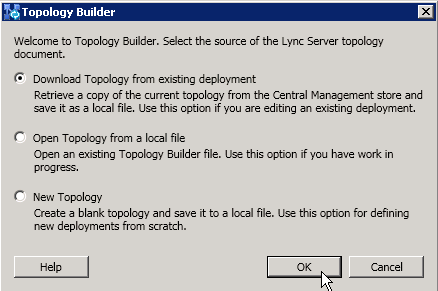
Download the Topology
Download Topology
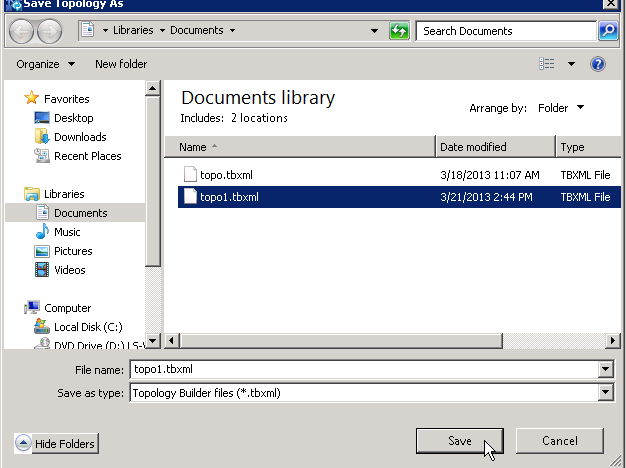
Specify a Filename
Specify Filename
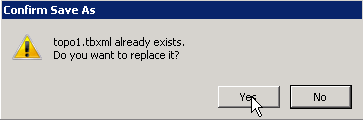
Confirm Changes
Confirm
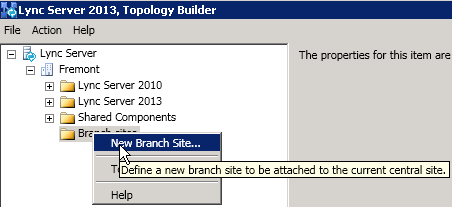
New Branch Site
Add a new Branch Site. In the example, Taveuni is the new remote branch.
Right-click on Branch Sites and select New Branch Site
New Branch Site
Enter the remote site identity
Remote Site Identity
Configure the site details
Site Details
New PSTN Gateway
Add sbc1000.sbc.net as Taveuni's PSTN Gateway.
New PSTN Gateway
Define PSTN Gateway
Define IP Address
Define Root Trunk
The RBA function requires media bypass, which, in turn requires TLS/SRTP. Later this document, the remote PSTN gateway will be re-configured from TCP/RTP to TLS/SRTP. Employing the simplier TCP/RTP model will help ease the implementation by providing a phased approach to the implementation.
Publish
Finally, Publish the newly configured topology.
Publish Topology
Publishing Wizard Complete
Lync Server Configuration
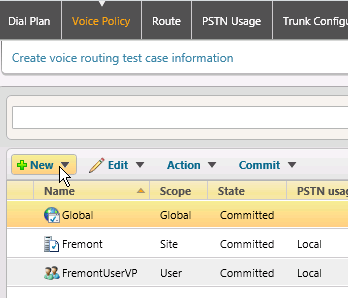
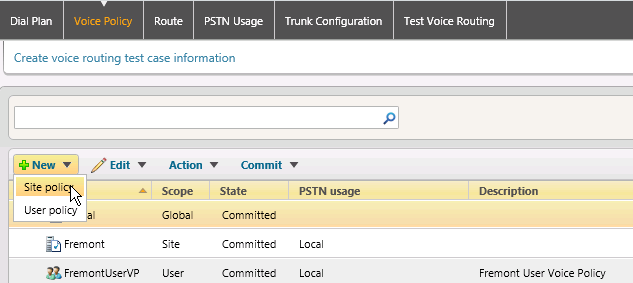
Create a new Site Voice Policy
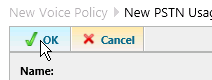
Click New
New
Add a Site Policy
Add Site Policy
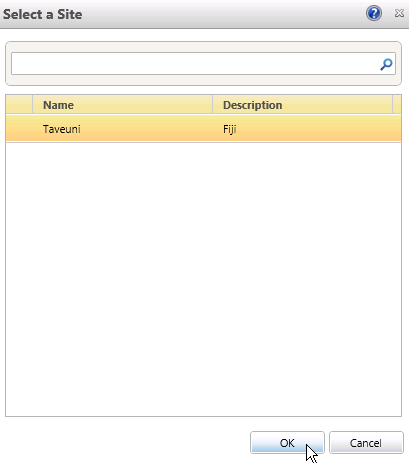
Select the remote site you just added to the Lync topology.
Select Remote Site
Add a new PSTN Usage
Add PSTN Usage
Supply a Name and Add a Route
Name and Route
Configure a call route pattern
Configure Call Route Pattern
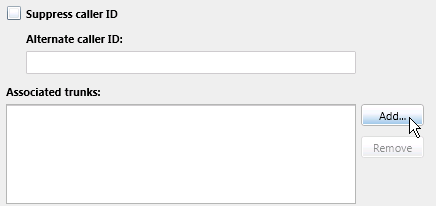
Add a Trunk
Add Trunk
Choose the newly added remote-network SBC
Select Trunk
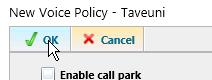
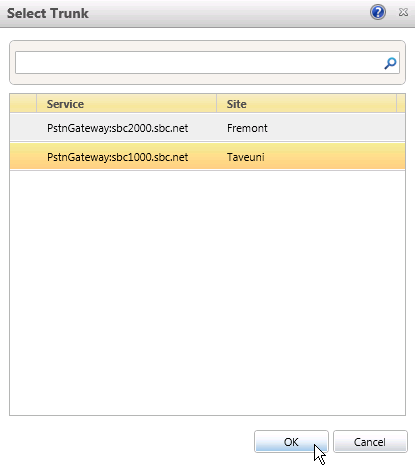
Click OKat each of the configuration layers
Configuration Level 1
Configuration Level 2
Configuration Level 3
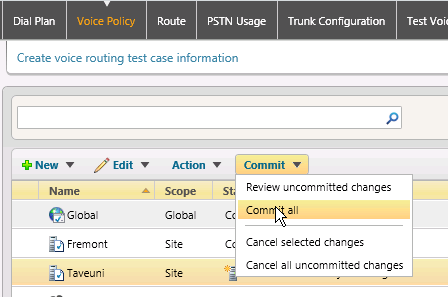
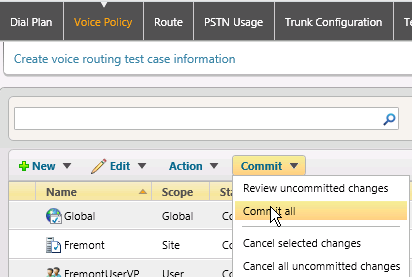
Commit New Site Voice Policy
Commit the changes to the Voice Policy
Click the Commit pulldown and Commit All
Commit All
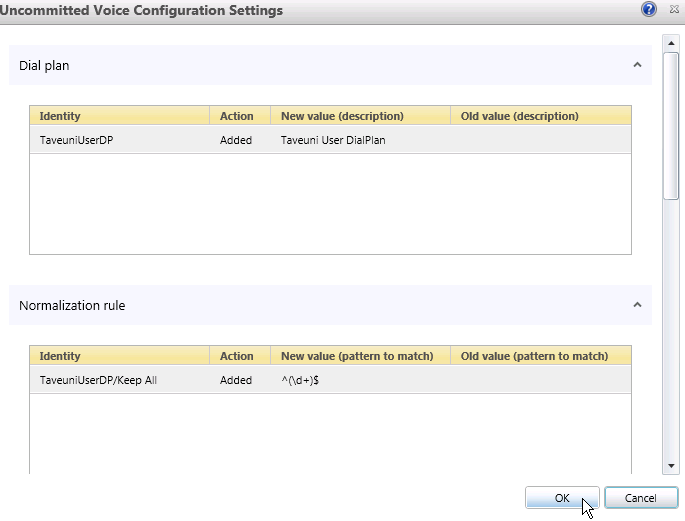
Click OK.
OK Configuration Settings
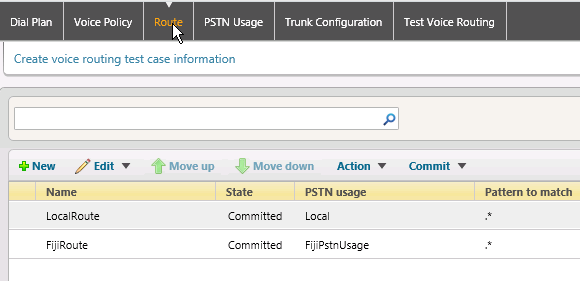
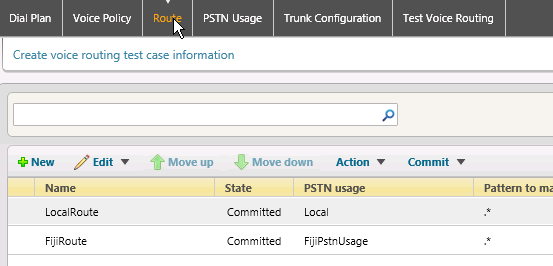
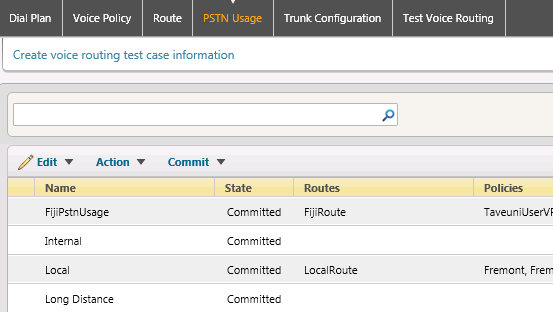
Verify Route and PSTN Usage
Verify the Route and PSTN Usages were added properly in the previous steps.
In the top navigation bar, click Route. Ensure that the route was added.
Ensure Route Added
In the top navigation bar, click PSTN Usage. Ensure that the PSTN Usage was added.
Ensure PSTN Usage Added
Create a User New Dial Plan
Similar to the previous steps, the following configuration adds User templates as opposed to Site templates.
To enable the RBA function, Lync users will have User-level Dial Plans and Voice Policies. The next steps create those policies.
Click Dial Plan in the top navigation. Click New_and select _New User Plan.
New User Dial Plan
Enter the information for your site and click OK.
OK Information
Create A New User Voice Policy
Create the Voice Policy that will be used with for the remote-network users.
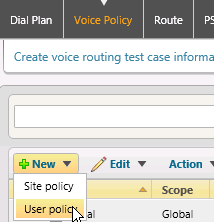
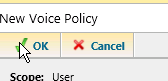
Click Voice Policy in the top navigation. Click New and select User Policy.
Voice Policy
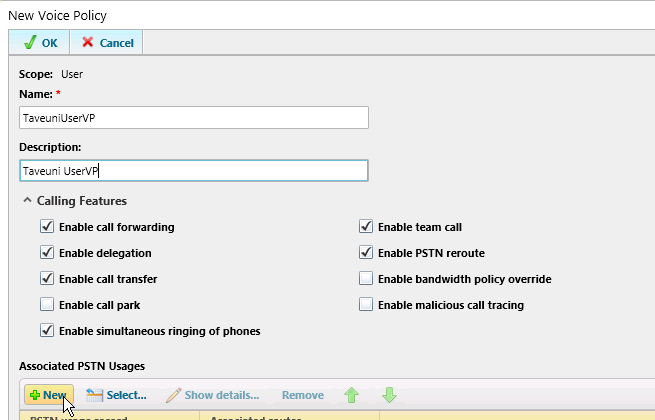
Fill in the form as shown using information for your particular installation.
Fill in Form
Click New under Associated PSTN Usages.
New Associated PSTN Usages
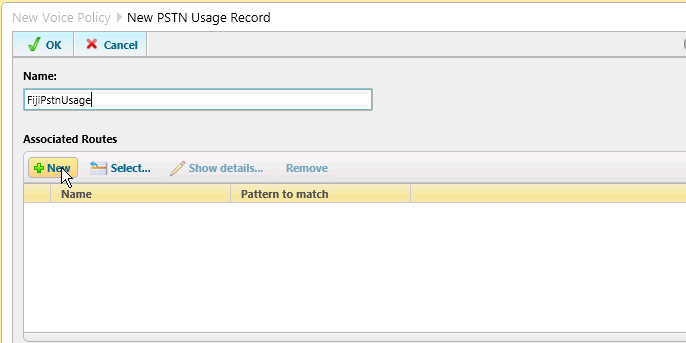
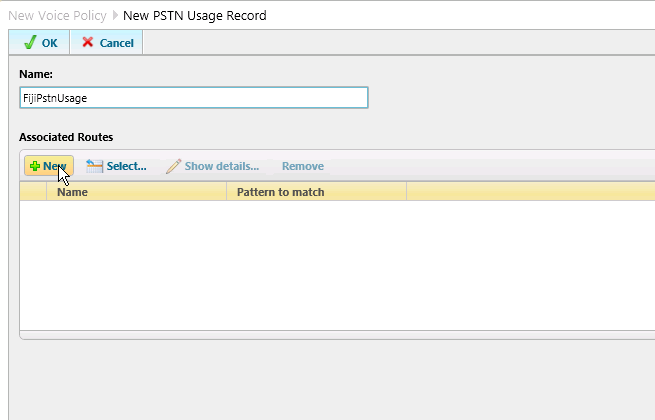
Create a New PSTN Usage
Create a PSTN Usage to be used with the User-level policies.
Create a New PSTN Usage record.
Create PSTN Usage Record
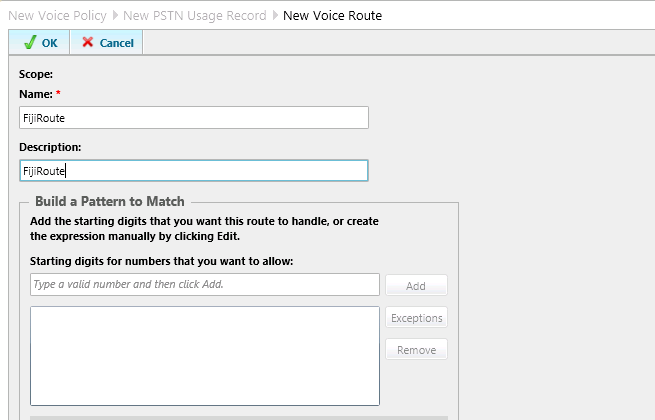
Enter your site-specific configuration information.
Enter Configuration Information
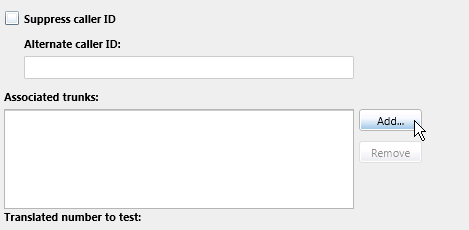
Click Add for Associated Trunk
Add Associated Trunk
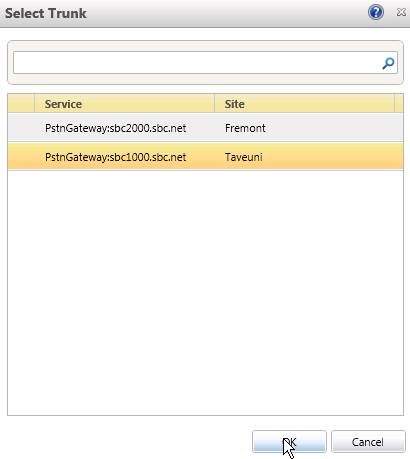
Select the remote-network SBC gateway
Select Trunk
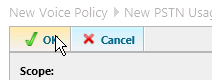
Click OKfor all the configuration layers.
Configuration Level 1
Configuration Level 2
Configuration Level 3
Commit Changes
Commit the additions to your Lync configuration.
Click the Commit pulldown, then select Commit All.
Commit All
Click OK.
OK Configuration Settings
Verify the Route was added.
Verify Route Added
Verify the PSTN Usagewas added.
Verify PSTN Usage Added
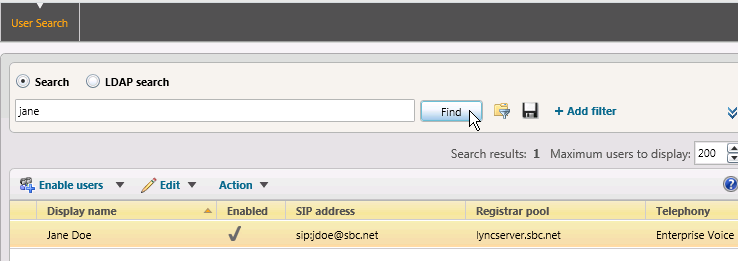
Add or Move a User into the New Remote Location
You will need to have a user homed to the remote-network location.
Click Users in the left-hand navigation. Enter the name of the user to move to the remote network and click Find.
Find User
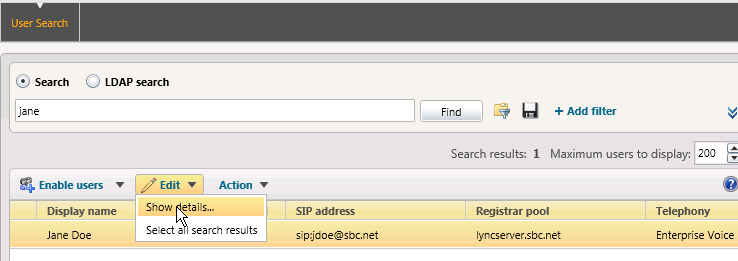
In the Edit pulldown, select Show Details.
Show Details
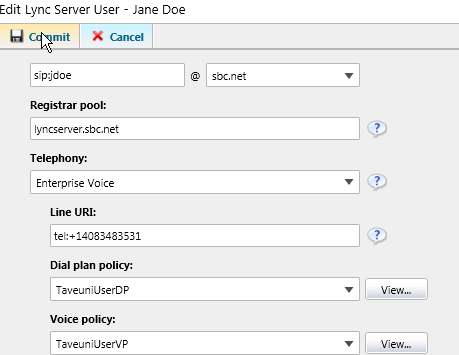
Set the Dial Plan and Voice Policy of the user to thos of the remote network Userpolicies.
Edit Lync Server User
Configure the Network Configuration
The Network Configuration controls how the CAC policies are applied. Follow the instructions to properly configure the Lync Network Configuration to interoperate with the RBA 3G4G link changes.
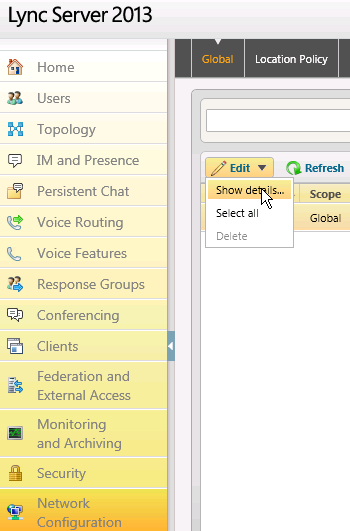
Click Network Configuration in the left-hand navigation. Click Global in the top navigation, click the Edit pulldown, and select Show Details.
Show Details
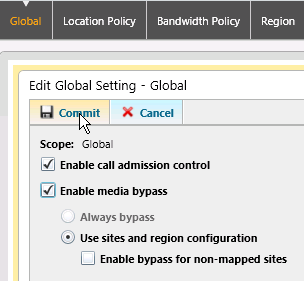
Ensure that the CAC and Bypass options are selected. Change the settings and commit, if necessary.
Edit Global Setting
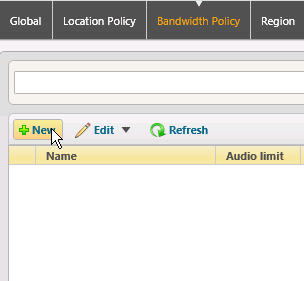
Create a New Bandwidth Policy
Create a Bandwidth Policy to be used to control the CAC from the RBA function.
Click Bandwidth Policy in the top navigation and select New.
New Bandwidth Policy
Enter the bandwidth specification for your remote network link, then click Commit.
Enter Bandwidth Specification
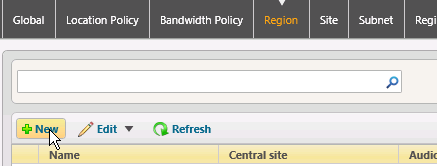
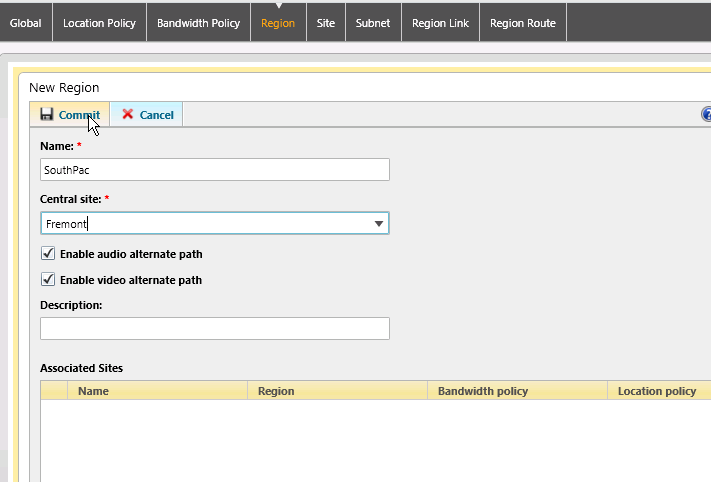
Create a New Region
Create regions to be used with the RBA feature. There will be a region for the HQ, as well as the remote-network.
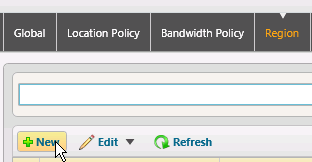
Click Region in the top navigation and select New.
New Region
Add a record for the remote region and Commit.
Remote Region Record
Click New to add the second region.
Add Second Region
Add a record for the HQ site and Commit.
HQ Site Record
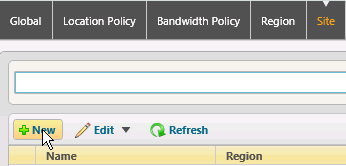
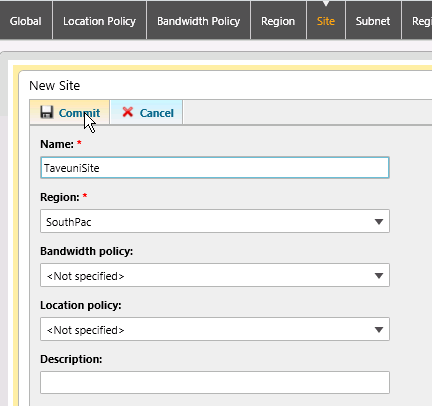
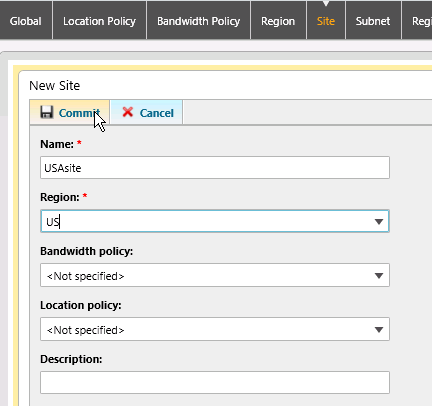
Create a new Site
Create sites to be used for the RBA function. Again, there will be a HQ site, as well as a remote site.
Click Site in the top navigation and select New.
New Site
Enter the information for your remote site. Click Commit.
Remote Site Information
Click New and enter the information for your HQ site. Click Commit.
HQ Site Information
Create New Subnets
IP addresses are used by the Lync Server to identify the origin of a Lync client. Create subnet records for both the HQ and remote network sites.
Click Subnet in the top navigation and select New.
New Subnet
Enter the IP network information for the remote network.
IP Network Information - Remote Network
Click Newand enter the IP network information for the HQ network.
IP Network Information - HQ Network
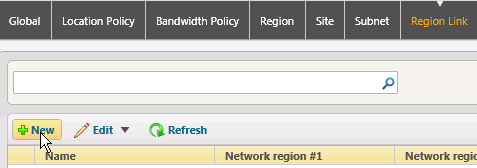
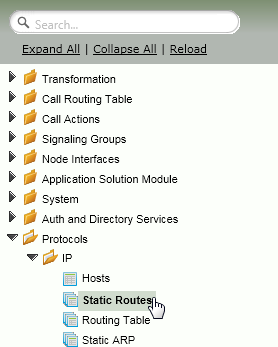
Create a Region Link
Create a Region Link between the sites.
Click Region Link in the top navigation and select New.
New Region Link
Using the pulldowns, select the HQ Region, the Remote Region and the Bandwidth Policy profile you previously created.
Select From Pulldowns
Create a New Region Route
Create a Region Route for the Region Link.
Click Region Route in the top navigation and select New.
New Region Route
Add the Network Regions as shown and add the newly created Region Link.
Add Network Regions
Domain Controller Configuration
The RBA ASM computer must be added to the Domain Controller as noted below. The computer must also be added to the RTCUniversalServerAdmins group.
On the Domain Controller, open the Server Manager
Open Server Manager
Add a new computer to Active Directory. You should have already selected a FQDN for the ASM module during the DNS Configuration section.
Add new Computer
Input the name of the ASM computer
Input Name of ASM Computer
Add the computer to the RTCUniversalServerAdminsgroup
Add Computer
Click OK
OK User or Group
Click OK
OK new Object
Configuring the RBA
Have you added the RBA as a computer in the Domain Controller and made it part of the RTCUniversalServerAdmins group?
Verify the ASM Board is Available using the Tasks Tab | Operational Statusselection
Verify ASM Board
Click Setup SBA in the left-hand navigation
Setup SBA
Click the ASM Config Tab and supply the information for your ASM. Click Apply.
Apply ASM Information
Click the Domain tab and supply the domain information for your network. Click OK. It will take a minutes to add the ASM to the domain and reboot.
Domain Tab
The Current Activity Panel will show when the domain join and rebooting processes are complete
Current Activity Panel
Click the Deploy SBA tab and select Prepare SBA. This will install the necessary components for the ASM to process the CAC changes supplied by the remote-network SBC. It will take approximately 30 minutes for the installation to complete.
Prepare SBA
The RBA requires only the Prep SBA step. The other SBA deployment steps are not required.
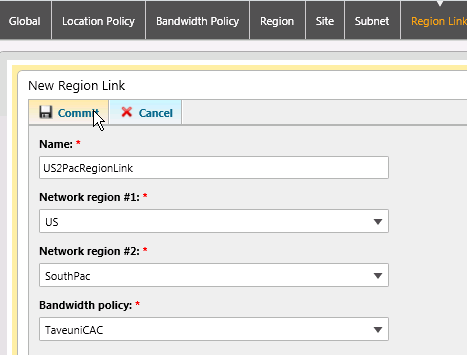
IP Routing
Ensuring the WAN and IPsec traffic use the appropriate routes is crucial to successful RBA failover.
SBC 1000 Static Routes
Click the Settings Tab and select Static Routes as shown in the diagram
Static Routes
On the remote-network SBC, add a Static IP Route
Add Static IP Route
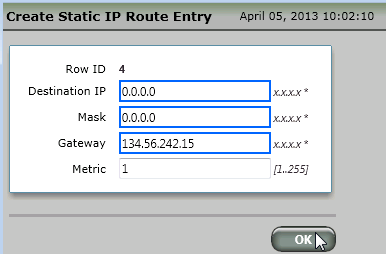
Create a default route that points to the WAN interface on the HQ SBC. Set the Metric to 1.
Create Default Route - Metric 1
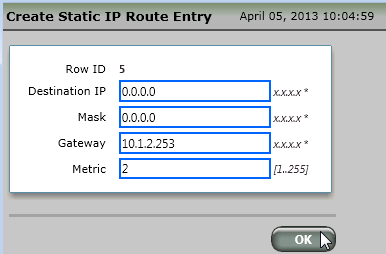
Create another default route that points to the IPsec interface on the HQ SBC. Set the Metric to 2.
Default routes are required for the automated routing failover to function. Only use default routes.
Create Default Route - Metric 2
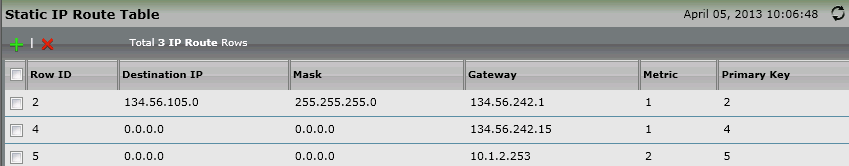
Verify the newly added static routes
Verify Static Routes
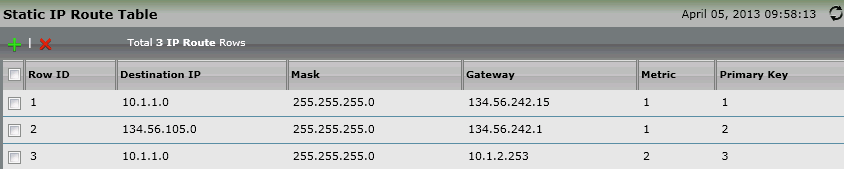
SBC 2000 Static Routes
On the HQ SBC, add specific subnet routes that point to the remote-network. One route should use the remote-network SBC's WAN connection (metric 1), the other should point to the Internet gateway (metric 2).
- When the WAN is up, the WAN-specific route to the remote-network will be used.
- When the WAN is down, the default Internet router will be used to send the traffic via the 3G4G carrier network.
Static IP Route Table
SIP Server Tables and Signaling Groups
Configure the SIP Servers and Signaling Groups for both HQ and remote-network SBCs.
SBC 1000 SIP Server Table
Click SIP Server Tablesin the left-hand navigation
SIP Server Tables
Add a SIP Server Table
Add SIP Server Table
Enter a description and click Apply.
Apply Description
Click the newly added SIP Server Table
Click New SIP Server Table
Enter the information for the HQ SBC
HQ SBC Information
SBC 1000 Signaling Groups
Click Signaling Groupsin the left-hand navigation. Add a Signaling Group for the HQ SBC.
Signaling Groups
Add the information to the newly added SG.
Add SG Information
SBC 2000 SIP Server Table
On the HQ SBC, add a SIP Server Table that points to the remote-network SBC
Add SIP Server Table
SCB 2000 Signaling Groups
On the HQ SBC, add a Signaling Group that points to the remote-network SBC
Add Signaling Group
On both SBCs, ensure that the Signaling Groups come Up
Ensure Signaling Groups Come Up - SBC 1000
Ensure Signaling Groups Come Up - SBC 2000
Verification
Verifying Routing
On the HQ SBC, verify that the Routing Table shows the route to the remote network using the WAN IP address of the remote SBC. In this case, the route to 10.1.2.0 (remote network) uses the remote SBC's 134.56.242.16 as the gateway.
Routing Table
Testing Connectivity over the WAN Link
Using a Command Prompt window from a PC on the remote network.
Ping the FQDN of the remote SBC. It should return remote-side private IP address (10.1.2.71 in this example).
C:\Users\Administrator.SBC>ping sbc1000.sbc.net Pinging sbc1000.sbc.net [10.1.2.71] with 32 bytes of data: Reply from 10.1.2.71: bytes=32 time<1ms TTL=64 Reply from 10.1.2.71: bytes=32 time<1ms TTL=64 Ping statistics for 10.1.2.71: Packets: Sent = 2, Received = 2, Lost = 0 (0% loss), Approximate round trip times in milli-seconds: Minimum = 0ms, Maximum = 0ms, Average = 0ms
Then ping the FQDN of the HQ SBC. It should return the IP address on the private side of the HQ network (10.1.1.74 in the example, not134.56.242.15)
C:\Users\Administrator.SBC>ping sbc2000.sbc.net Pinging sbc2000.sbc.net [10.1.1.74] with 32 bytes of data: Reply from 10.1.1.74: bytes=32 time=1ms TTL=63 Reply from 10.1.1.74: bytes=32 time<1ms TTL=63
- Ping the FQDN of the Lync Server
- Ping the FQDN of the Domain Controller
- Ping the FQDN of the DNS Server
- Ping the FDQN of the RBA
All the returned IP addresses must be on the private-side of the HQ network (e.g. 10.1.1.x)
From a PC on the HQ side of the network
Ping the FQDN of the Remote SBC. It should return a remote LAN IP address.
C:\Users\Administrator>ping sbc1000.sbc.net Pinging sbc1000.sbc.net [10.1.2.71] with 32 bytes of data: Reply from 10.1.2.71: bytes=32 time=5ms TTL=63 Reply from 10.1.2.71: bytes=32 time=3ms TTL=63 Reply from 10.1.2.71: bytes=32 time=3ms TTL=63 Reply from 10.1.2.71: bytes=32 time=3ms TTL=63 Ping statistics for 10.1.2.71: Packets: Sent = 4, Received = 4, Lost = 0 (0% loss), Approximate round trip times in milli-seconds: Minimum = 3ms, Maximum = 5ms, Average = 3ms
- Ping a PC on the remote LAN. Check that the default router on the remote LAN PC is set to the (remote) SBC's LAN interface address (10.1.2.71 in the example).
Test a Lync to Lync Call
At this point you should be able to call Lync-to-Lync over the WAN.
Creating the IPsec Tunnel
Use the following steps to configure an IPsec tunnel between the remote and HQ SBCs.
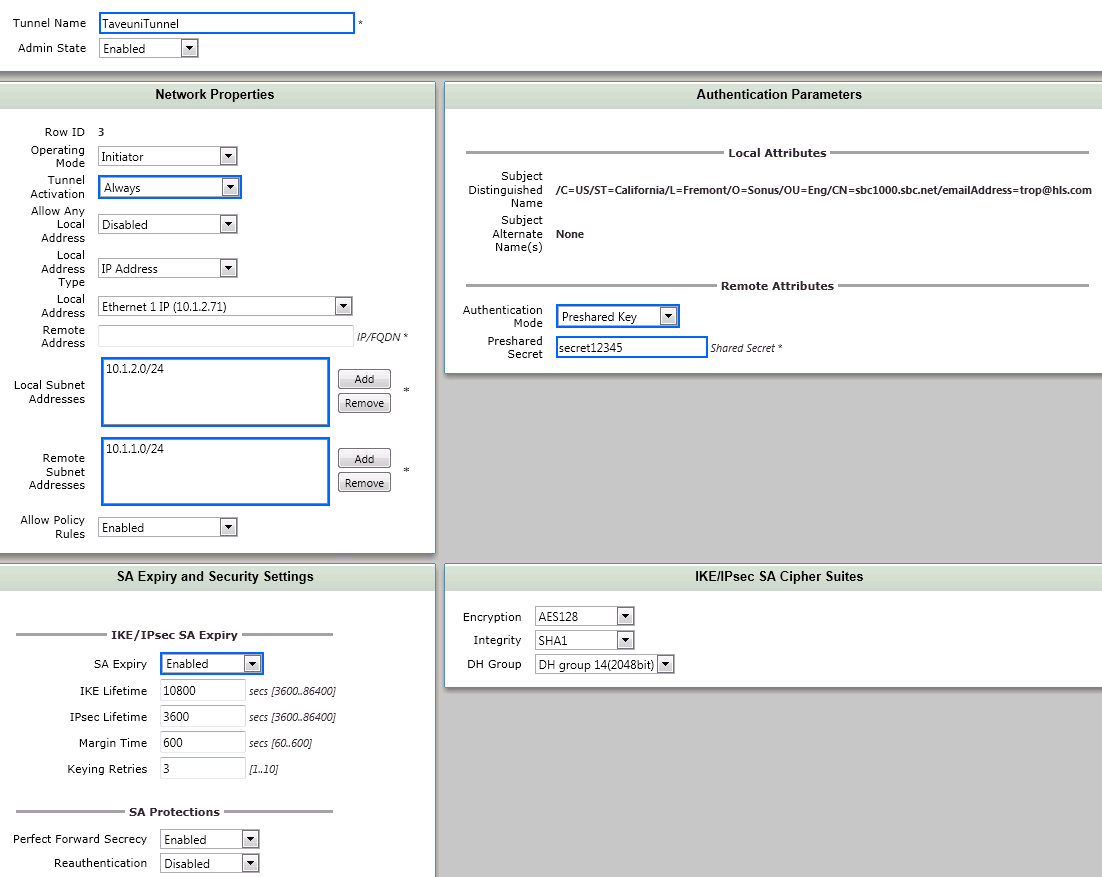
SBC1000 IPsec Configuration
The following steps configure the remote SBC to generate an IPsec tunnel to the HQ SBC when the WAN is down.
Click IPsec | Tunnel Tablein the left-hand navigation.
Tunnel Table
Add a Tunnel Table
Add Tunnel Table
- Enter the configuraton information for your IPsec tunnel.
- The Local Subnet Address must be programmed with IP information for the remote network.
The Remote Subnet Addressmust be programmed with IP information for the HQ network.
Enter Configuration Information
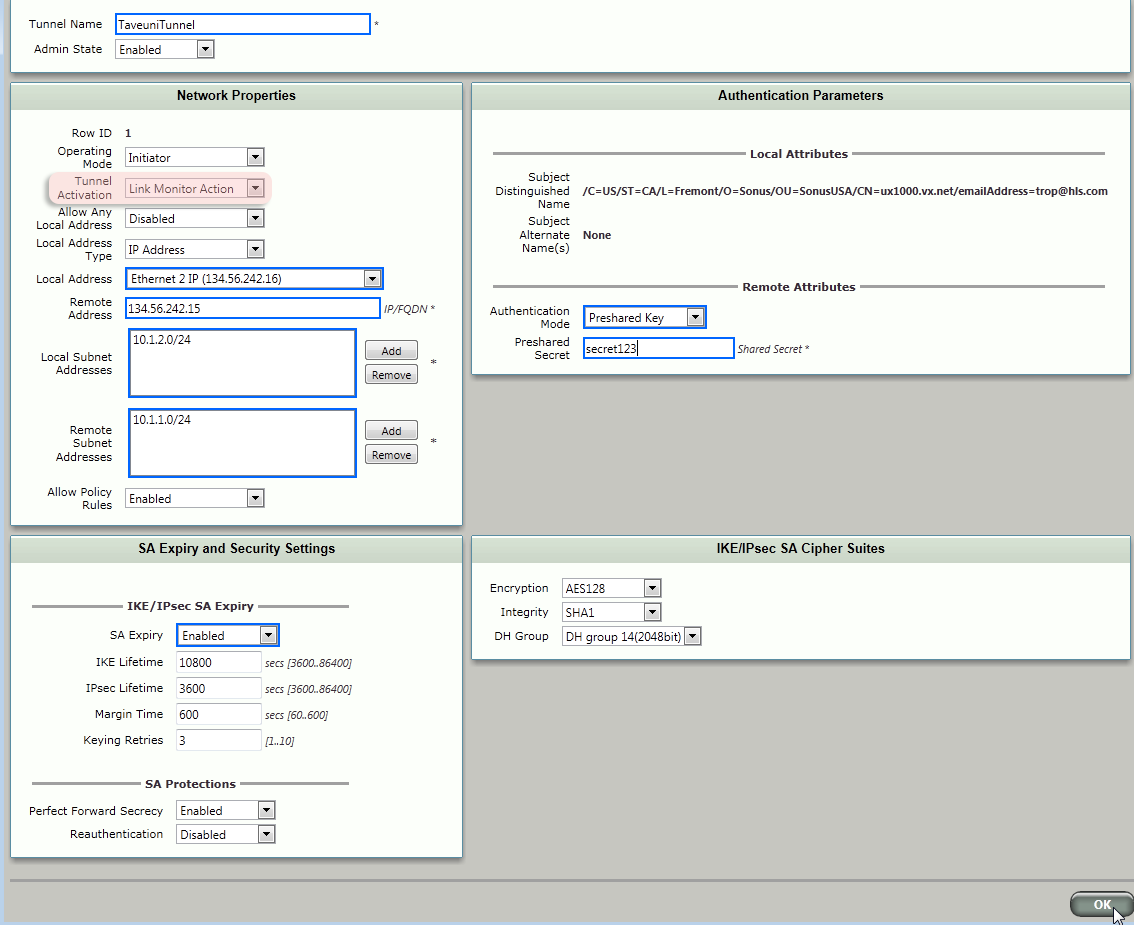
SBC2000 IPsec Tunnel Configuration
The following steps configure the HQ SBC to receive an IPsec tunnel from the remote SBC when the WAN is down.
Configure an IPsec tunnel on the HQ SBC with information appropriate to your network. On the HQ SBC, the Local Subnet Address is the HQ network, the Remote Subnet Addressis the remote network subnet(s).
Create IPsec Tunnel Entry
Verification
In this section you will test the IPsec tunnel to ensure connectivity exists when the WAN link is down.
Preparing for Verification
- Pull the cable from the WAN port on the Remote SBC. You must pull the cable from the WAN port on the Remote SBC for this verification step. Downing the WAN port results in automatically disabling the WAN IP route.
Manually remove the WAN Route from the HQ SBC
Remove WAN Route
On the Remote SBC, use the refresh button to verify the Service Status is Link Up.
Verify Service Status
The Signaling Groups should come back up after the IPsec tunnel is esablished.
Signaling Groups - SBC 1000
Signaling Groups - SBC 2000
Verifying PC Connectivity
From a remote LAN PC, ping the FQDN of the HQ SBC. Note that the Round Trip Time (time) is much longer than that for the ping over the WAN link.
root@sbc1000:~# ping sbc2000.sbc.net PING sbc2000.sbc.net (10.1.1.74) 56(84) bytes of data. 64 bytes from 10.1.1.74: icmp_req=1 ttl=64 time=76.2 ms 64 bytes from 10.1.1.74: icmp_req=2 ttl=64 time=75.4 ms ^C --- sbc2000.sbc.net ping statistics --- 2 packets transmitted, 2 received, 0% packet loss, time 1000ms
- Make a Lync call from between remote and HQ lync clients. The clients should ring and answer.
Re-add the HQ SBC WAN Route
Before proceeding, replace the HQ SBC WAN route to the remote SBC.
Create Static IP Route Entry
Configuring for Automated Switchover
With the successful testing of the static IPsec tunnel, it is time to make the tunnel dynamic so that the 3G4G link is only used activated when the WAN is down.
Modify the Remote SBC IPsec Tunnel Activation to Link Monitor Action and click OK.
Modify Tunnel Activation
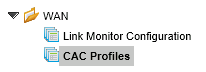
SBC 1000 CAC Profiles
The CAC profiles are transmitted to the Lync Server via the HQ SBC when the WAN transitions link states.
Create the CAC Profiles on the Remote SBC
Click WAN in the left-hand navigation and select CAC Profiles.
CAC Profiles
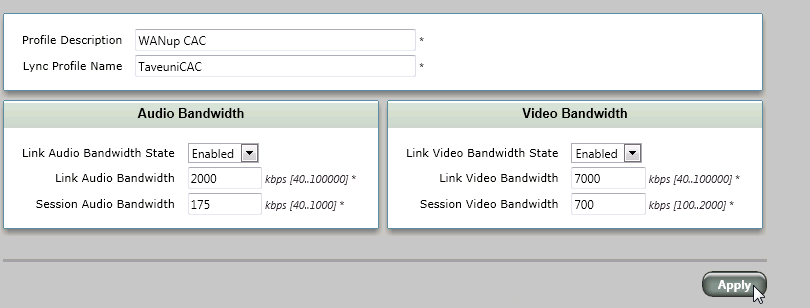
Create a profile for the WAN up situation. Set the bandwidths according to your desired WAN link configuration and capacity. Click Applywhen finished.
Create Profile for WAN Up
Now, create a CAC profile for WAN down. Setting the Bandwidth State to Disabledresults in any HQ<>remote-network calls being routed over the PSTN.
Create CAC Profile for WAN Down
SBC 1000 Link Monitor Configuration
The Link Monitors provide the ability for the remote SBC to know whether the WAN is up and available.'
Click Link Monitor Configuration
Link Monitor Configuration
Add a monitor to monitor the public IP interface of the HQ SBC and click Apply.
Monitor Public IP Interface
Add a monitor to monitor the 3G4G router port. Associate this Link Monitor with the IPsec Tunnel you recently created. With this link activated (due to WAN down), the IPsec tunnel will be automatically started.
Monitor 3G4G Router Port
Verification
Verify the following tables on the remote SBC
Verify CAC Profile Table
Verify Link Monitor Configuration Table
SBC 2000 Link Monitor Configuration
Configure a Link Monitor on the HQ SBC in order that it may dynamically adjust its internal routing table when the WAN link switches. The Link Monitor is configured to monitor the WAN side only.
Create a fake CAC entry. This entry will be ignored for purposes of bandwidth adjustment.
Create Fake CAC Entry
Create a Link Monitor that monitors the WAN interface of the remote SBC.
Create Link Monitor
Verification
Verify the condition of the routes and IPsec links.
WAN Link Up
HQ SBC
With the WAN link up, the HQ SBC routing table and Link Monitor should resemble the following.
HQ SBC Routing Table
HQ SBC Link Monitor
Remote SBC
With the WAN link up, the remote SBC's routing table should point to the WAN interface on the HQ SBC.
Routing Table - Point to WAN Interface
The Link Monitor Table should be Readyon the WAN link
Link Monitor Table - Ready
The IPsec tunnel should be Link Down
IPsec Tunnel - Link Down
Lync Server
Verify the Lync Bandwidth Profile using the Bandwidth Policy Service Monitor, which is installed as a component of the optional Lync Server Resource Kit (available from the Microsoft Lync Server website).
Open Windows Explorer to C:\Program Files\Microsoft Lync Server 2013\ResKit\BandwidthPolicyServiceMonitor and select PDPMonUI.exe.
Select PDPMonUI.exe
Expand the server name in the left-hand navigation and select the expanded server.
Expanded Server Name
Click the Topology Infotab
Topology Info tab
Verify the bandwidth settings are for the WAN up values.
Verify Bandwidth Settings
Lync Clients
Test a call between a HQ and Remote Lync client. Calls between HQ and Lync clients should connect directly over the WAN without need for a PSTN connection.
WAN Link Down
Downing the WAN Link should result in the following status. With the WAN link down, verify your implementation to the following:
HQ SBC Status
On the HQ SBC, the WAN Link Monitor should show down and the IPsec tunnel up.
Link Monitor Service Status
IPsec Tunnel Service Status
Remote SBC Status
On the Remote SBC, the Link Monitor should show the 3G4G link up, the WAN link down, and the IPsec tunnel up.
3G4G Link Up and WAN Link Down
IPsec Tunnel Link UP
Lync Server
Within two or three minutes, the Bandwidth Policy should automatically update to the WAN down bandwidth values.
Bandwidth Policy Update
Lync Clients
Test a call between a HQ and Remote Lync client. In the WAN down condition, you should be able to call between HQ and Remote Lync clients. The calls should utilize the PSTN connection between the SBCs.
Remember, for Lync implementations, the SBC is a PSTN gateway for the Lync Server. When in the WAN down condition, the Lync server will send calls to the remote PSTN (SBC) gateway. You must configure the customary SBC routes and transformation tables that would be used for calls to/from Lync.
Setting the Remote SBC to TLS
The remote SBC must beconfigured to TLS/SRTP in order for the remote Lync clients to send calls over the PSTN during a 3G4G failover. The following steps will assist you in configuring the Lync Server and remote SBC for TLS/SRTP.
On the Lync Server, start the Topology Builder and Edit Properties for the remote site Trunk.
Edit Properties
Change the port and configuration to support TLS as shown.
Change Port and Configuration
Publish the topology.
Publish Topology
Certificate for the SBC
Certificates are required for TLS/SRTP functionality. The following steps will assist you in installing certificates on the remote SBC.
Click the Taskstab.
Tasks Tab
Click Lync Setupin the left-hand navigation
Lync Setup
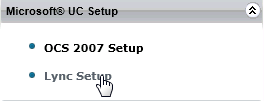
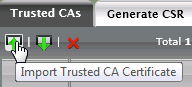
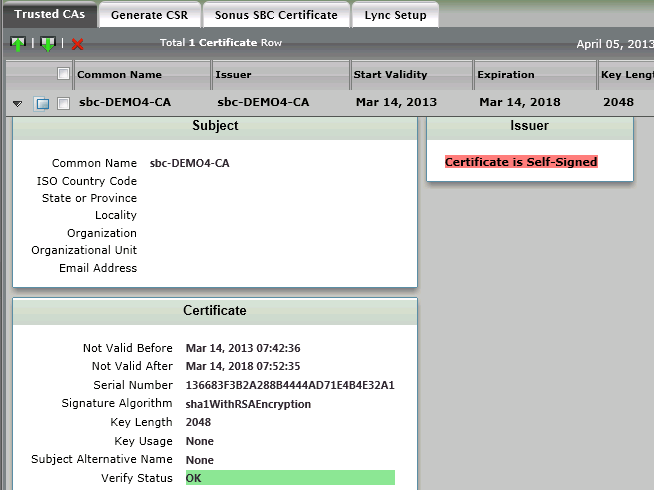
Obatin the root certificate from your network administrator and copy it to your PC. From the webui, click Import Trusted CA Certificateas shown.
Import Trusted CA Certificate
Set the Mode to File Upload and Browseto find the file containing the root certificate.
CA Certificate File Upload
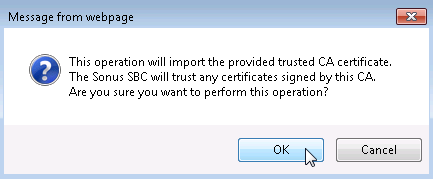
Click OKto import the root certificate.
Import Root Certificate
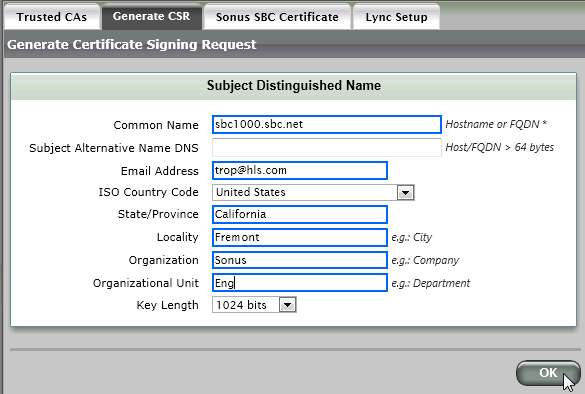
Click the Generate CSRto generate a certificate request for the SBC. You will send this certificate request to be signed by the your certificae authority.
Generate CSR
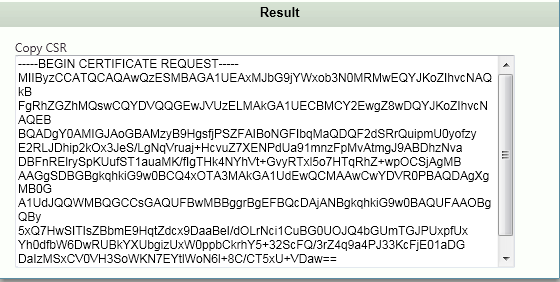
Copy and paste the certificate request into a file and send it to your root certificate authority for signing.
Result
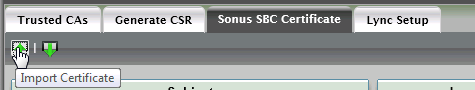
When the signed certificate is returned, click the Sonus SBC Certificatetab and import the certificate.
Import Certificate
Set the Mode to File Upload and Browseto find the file containing the SBC certificate.
SBC Server Certificate File Upload
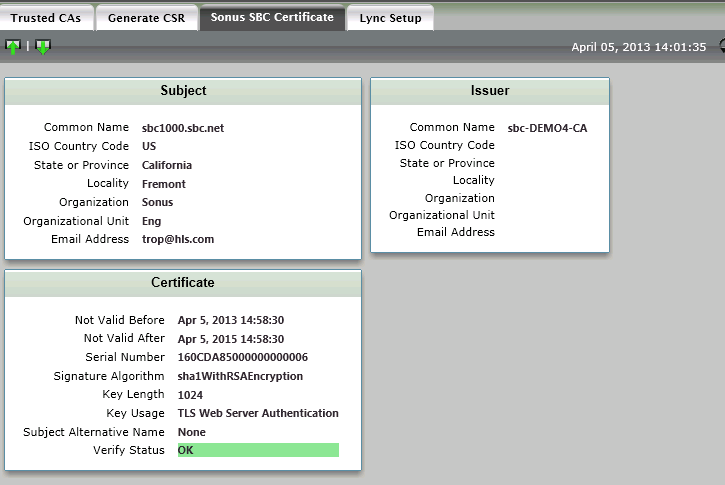
Verify the SBC and root certificates
Sonus SBC Certificate
Trusted CAs
Setting the SIP Server and Signaling Group for TLS/SRTP
On the remote SBC, set/create the Lync Server SIP Server as shown.
Set/Create Lync Server SIP Server
Set/create a Lync Server Signaling Group as shown.
SIP Signaling Group Details
The Lync Server Signaling Group should come up
Lync Server Signaling Group - Up
RBA Data Flows
WAN Up Flow
WAN Up Flow
WAN Down Instant Message Flow
WAN Down Instant Message Flow
WAN Down Lync-to-Lync Call Flow
WAN Down Lync-to-Lync Call Flow
- As an IP router, the SBC forwards the SIP request from the remote Lync to the Lync Server
- Lync server sends a SIP request to the remote SBC (as a SIP --> PSTN gateway)
- Remote SBC dials the HQ SBC via PSTN
- HQ SBC (as a SIP Gateway) sends a SIP request to the Lync server
- Lync Server sends SIP Request to the HQ Lync client
- Remote Lync client audio bypasses directly to the remote SBC.
Troubleshooting
This section contains troubleshooting tips and suggests for various issues that may arise during RBA implementation.
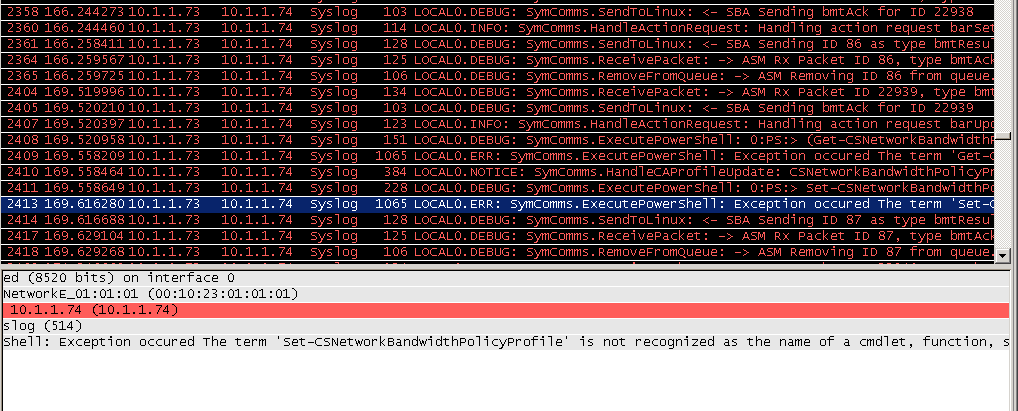
Prepare SBA not run
A wireshark trace which shows an exception due to an unrecognized cmdlet is likely due to the Prep SBA function not being executed. Review the Configuring the RBA section of this document.
Prep SBA Function Not Executed
RBA computer not a member of RTCUniversalServerAdmins group
Should the CAC bandwidths fail to change when the active link is switched between the WAN and the 3G4G link and this message appears in the RBA system Event Log, then the RBA computer (ASM) is not a member of the RTCUniversalServerAdmins group. See the Domain Controller Configuration section of this document.
Syslog message: LOCAL0.ERR: SymComms.ExecutePowerShell: Exception occured Cannot open database "xds" requested by the login. The login failed.\r\nLogin failed for user 'SBC\RBA1$'.. Could not connect to SQL server : [Exception=
A gpresult comamnd run from directly from the RBA computer (ASM) which shows that the computer is not a member of the RTCUniversalServerAdmins group.
C:\Users\Administrator>gpresult /R
Microsoft (R) Windows (R) Operating System Group Policy Result tool v2.0
Copyright (C) Microsoft Corp. 1981-2001
Created On 4/5/2013 at 9:07:11 AM
RSOP data for SBC\Administrator on RBA1 : Logging Mode
-------------------------------------------------------
OS Configuration: Member Server
OS Version: 6.1.7601
Site Name: Default-First-Site-Name
Roaming Profile: N/A
Local Profile: C:\Users\Administrator
Connected over a slow link?: No
COMPUTER SETTINGS
------------------
CN=rba1,CN=Computers,DC=sbc,DC=net
Last time Group Policy was applied: 4/5/2013 at 8:06:36 AM
Group Policy was applied from: demo4.sbc.net
Group Policy slow link threshold: 500 kbps
Domain Name: SBC
Domain Type: Windows 2000
Applied Group Policy Objects
-----------------------------
Default Domain Policy
The following GPOs were not applied because they were filtered out
-------------------------------------------------------------------
Local Group Policy
Filtering: Not Applied (Empty)
The computer is a part of the following security groups
-------------------------------------------------------
System Mandatory Level
Everyone
BUILTIN\Users
NT AUTHORITY\SERVICE
CONSOLE LOGON
NT AUTHORITY\Authenticated Users
This Organization
BITS
CertPropSvc
EapHost
hkmsvc
IKEEXT
iphlpsvc
LanmanServer
MMCSS
MSiSCSI
RasAuto
RasMan
RemoteAccess
Schedule
SCPolicySvc
SENS
SessionEnv
SharedAccess
ShellHWDetection
wercplsupport
Winmgmt
wuauserv
LOCAL
BUILTIN\Administrators
Service Status Stays Yellow
Check the routing table on the remote SBC. The remote SBC must use default routes (0.0.0.0/0) rather than network routes.
Link Monitor Configuration Table
Route Table With No Default Routes
OPTIONS with Carrier's IP address
If the HQ SBC receives OPTIONS with the 3G4G carrier's source IP address, then the configured routing or hosts are incorrect. Make sure that the SBC are configured to use only the LAN interface addresses.
[2012-04-04 17:01:32,550] 4202 0031 com.sonus.sbc.sip DEBUG (TransportLayer.cpp:810) - DataReadCB: Received message on [134.56.242.15]:5060 from [166.137.185.63]:34539 size=469, data: 0x2beb24, current chunk: 0
[2012-04-04 17:01:32,550] 4203 0030 com.sonus.sbc.sip TRACE (SipMessage.cpp:98) - SipMessage: ctor msg 0x320918 35789
[2012-04-04 17:01:32,551] 4204 002f com.sonus.sbc.sip TRACE (MessageHeader.cpp:301) - decodeLite: headerType=Via, commaDetection=1
[2012-04-04 17:01:32,551] 4205 002e com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type Allow
[2012-04-04 17:01:32,551] 4206 002d com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type Call-ID
[2012-04-04 17:01:32,551] 4207 002c com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type Content-Length
[2012-04-04 17:01:32,551] 4208 002b com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type CSeq
[2012-04-04 17:01:32,551] 4209 002a com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type From
[2012-04-04 17:01:32,551] 4210 0029 com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type Max-Forwards
[2012-04-04 17:01:32,551] 4211 0028 com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type Supported
[2012-04-04 17:01:32,551] 4212 0027 com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type To
[2012-04-04 17:01:32,551] 4213 0026 com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type User-Agent
[2012-04-04 17:01:32,551] 4214 0025 com.sonus.sbc.sip TRACE (SipMessage.cpp:634) - decodeHeaders: SIP message Header type Via
[2012-04-04 17:01:32,551] 4215 0024 com.sonus.sbc.sip DEBUG (SipMessage.cpp:1202) - decodedLength:469 decoded 0x320918:
[2012-04-04 17:01:32,551] 4216 0023
OPTIONS sip:sbc2000.sbc.net:5060 SIP/2.0
Allow: INVITE, ACK, CANCEL, BYE, UPDATE, NOTIFY, OPTIONS, REFER, REGISTER
Call-ID: call-71280200-0000-0010-0C13-0@10.1.2.71
Content-Length: 0
CSeq: 123 OPTIONS
From: <sip:Anonymous@10.1.2.71:5060>;tag=8638f210-1
Max-Forwards: 70
Supported: replaces,update,100rel
To: <sip:Anonymous@sbc2000.sbc.net:5060>
User-Agent: SONUS SBC1000/2000 3.0.0v222 UX
Via: SIP/2.0/UDP 10.1.2.71:5060;branch=z9hG4bK-UX-8638-f210-0180
[2012-04-04 17:01:32,552] 4217 0022 com.sonus.sbc.sip TRACE (sipApplication.cpp:1264) - tlDataReceived: No errors found. Processing message.
[2012-04-04 17:01:32,552] 4218 0021 com.sonus.sbc.sip TRACE (sipSignalingGroup.cpp:1522) - {SG(1) 0x30b808} CanAccept: Reject msg: call=1, transport=0, filter=0 localPort=0
[2012-04-04 17:01:32,552] 4219 0020 com.sonus.sbc.sip DEBUG (sipSignalingGroupConfig.cpp:713) - getBestSubnet: 166.137.185.63 - 0.0.0.0
[2012-04-04 17:01:32,552] 4220 001f com.sonus.sbc.sip DEBUG (sipSignalingGroupConfig.cpp:713) - getBestSubnet: 166.137.185.63 - 166.137.185.63
[2012-04-04 17:01:32,552] 4221 001e com.sonus.sbc.sip DEBUG (sipSignalingGroupConfig.cpp:713) - getBestSubnet: 166.137.185.63 - 0.0.0.0
RBA Command Working Properly
This wireshark trace shows a properly working cmdlet to change the CAC bandwidth policies.
Wireshark Trace
rev 0.2